Permission Denied Please Try Again Raspberry Pi Pi Bakery
Get SSH Working on a Raspberry Pi four
Secure crush (SSH) is a very handy tool for connecting to your Raspberry Pi, peculiarly if you practise not have a monitor, keyboard and mouse at your disposal. Think of SSH as a remote log-in which allows you to work on another system potentially far-removed from the comfort of your easy chair, function chair, standing desk, granite slab or whatsoever other work area you chose.
Wait, hold on: I might take heard about SSH simply what is this 'Raspberry Pi', anyway? Love readers, allow me to present:

Call up of the Raspberry Pi equally a tiny computer running Raspbian, a flavour of Linux. A tasty flavor, I might add! Considering of the Pis' Linux roots, many of the steps in this article therefore utilise to configuring SSH on a much bigger host; Debian boxes to be specific. The instructions should work well with other types of Linux operating systems just your mileage may vary.
There are a few catchy things I encountered when I starting time attempted to set up secure beat on my RPi. SSH is the gift that keeps on giving! I ran into several difficulties during my intial setup and I suspect other users will encounter like issues. There are a decent number of rather straightforward tutorials that explain how to SSH into a RPi including this 1 and that one. Along with these tutorials I institute that I had to dig around a couple of discussion posts when I ran into difficulties. I hope that this article will aid others in their quest to connect to a Pi via SSH!
Server Setup
First things starting time: Despite my conventionalities that I'm a top contender for Virtually Consequent Author on the Planet, I may not ever exist. Words like 'Host', 'Raspberry Pi', 'RPi' and 'Pi' are used interchangeably throughout this article. Some other matter I will point out before getting into the nitty-gritty of SSH is you lot must have a few $.25 and pieces beforehand. Similar a functional Raspberry Pi that is powered upward and connected to your network, preferably with an Ethernet cablevision. And a static IP assigned past your router to your Pi. And a client machine that is besides ideally assigned a static IP and is connected to your local network with, you guessed information technology, an Ethernet cablevision. And… a working installation of Raspbian on your Pi. Experience free to subsitute a nuance of WiFi in place of your Ethernet cables provided all your devices support it.
You will also desire to change any items marked with <..> to conform your particular situation.
Make sure your SuperUser has a strong countersign earlier proceeding any farther! The default password when logging into a Raspberry Pi for the first time needs to exist changed to something stronger before you make additional changes.
Assuming you take all of the above pieces, be sure to perform an initial fix-up of SSH once you are logged into Raspbian. You will want to verify SSH enabled get-go and foremost. Navigate to the 'raspberry' icon in the card (unremarkably at the top-left) and select Preferences, Raspberry Pi Configuration. Enter your SuperUser countersign when prompted. In the Interfaces tab, select Enable for SSH. Close the carte du jour.
If for some strange reason yous do non take SSH installed on your Raspberry Pi you can apply the following steps to install it; see this post for details. Within a terminal on your Pi type:
sudo apt install openssh-server
Ostend SSH is running using the following control:
sudo service ssh status
Client Setup
When connecting to your Rasberry Pi for the first time via SSH, run the following command from your client:
ssh -v -o PreferredAuthentications=password -o PubkeyAuthentication=no pi@<pi_IP>
Provided this is the first time on this car that you have attempted to SSH to your Pi, you should get a prompt asking you whether or not yous trust the host, yous tin can say yes to this. Farther details are available at this Raspberry Pi forum.
Upon entering your password, yous will likely get the dreaded:
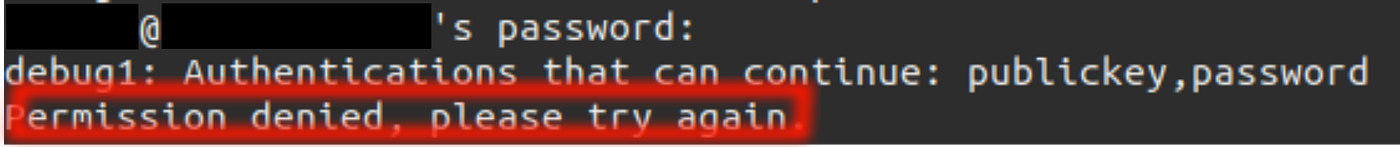
Well then.
Here is the office where I get a little fist-shakey at my Pi. Merely do not dispair, there are some things we can practise to get SSH working.
Setup — Digging Further
You will want to have your host machine shut-down and continued to a monitor, keyboard and mouse for these side by side parts.
With periphirals connected and your host (Pi) restarted, go ahead and log-in. Pull up a terminal session. You tin can now audit your host'south logs for whatsoever error letters. SSH is rather repose when it comes to informing users of errors. Whatsoever such errors printed to the final may appear vague; this is in all likelyhood to prevent malicious users from getting the upper mitt and gaining access to your arrangement. No one wants that. Especially me!
Audit your SSH log file using the following command:
sudo nano /var/log/auth.log
Once you take examined your log file for errors related to SSH, you tin can also inspect the settings file for the SSH daemon. From the last on your host blazon:
sudo nano /etc/ssh/sshd_config
Be sure you are editing sshd_config, NOT ssh_config; come across this post.
Enable PublicKey
This file should contain a number of configuration parameters that yous can tweak to get your SSH working. Before proceeding further, I recommend making a backup copy of this file. You know, in the outcome you brand a mistake and accept to revert dorsum to a previous good copy. Or, the globe explodes. But probably if you have to revert back. Possibly. Once a back-up copy is made and you are back in Nano to edit your sshd_config file , you can un-annotate the following line:
# Modified YYYY-MM-DD by <author>.
PubkeyAuthentication yes
Uncomment the PasswordAuthentication line as well:
# Modified YYYY-MM-DD past <writer>.
PasswordAuthentication yeah
When making changes to your configuration files I recommend inserting a comment directly in a higher place the change, along the lines of:
# Modified YYYY-MM-DD by <writer>.
AllowUsers and AllowGroups
Another setting to check is that the correct user can access SSH. This stride had me scratching my head for quite a while! The default configuration may take an AllowGroups line as follows:
AllowGroups root ssh
For the purpose of this tutorial I recommend that y'all annotate out the AllowGroups line to limit the configuration for the SSH daemon to a single user.
Add an AllowUsers line directly below PasswordAuthentication every bit follows:
# Modified YYYY-MM-DD by <author>.
PasswordAuthentication yep
# Added YYYY-MM-DD past <author>.
AllowUsers pi
Comment-out AllowGroups if it is nowadays:
# Changed on YYYY-MM-DD by <author>.
# AllowGroups …
Feel free to alter the username to any name you have set upwardly for your user although be sure that this user is given privileges for SSH. For an initial setup, I notice it easier to apply the default user pi for troubleshooting. Further details on AllowUsers and AllowGroups equally well as their precedence can be found at this helpful link.
You lot can further specify the host that your user is immune to connect with. Instead of specifying the user, endeavor specifying <user>@<remotehost> in your list of AllowUsers as suggested by this article:
AllowUsers pi@raspberrypi
Disable PermitEmptyPasswords
Although it is a bad do, a Linux system administrator can create a user account with no countersign. That means remote connection requests from that account will have no password to check against. Those connections will be accustomed but unauthenticated. The default settings for SSH volition likely take connectedness requests without passwords. We tin can change that very easily, and ensure all connections are authenticated past uncommenting the following line:
#PermitEmptyPasswords no
Becomes:
PermitEmptyPasswords no
Once you are satisfied with the changes, become alee and save the file by hitting cntl-o then cntl-10 to leave.
All good, right? Can nosotros start SSH-ing yet?
I retrieve information technology is prounounced 'shush-ing'. And the answer is No.
Setup — Almost At that place
Back in the final on your Pi, in order for all of the configuration changes to take effect you first demand to restart your SSH daemon on your server:
sudo systemctl restart ssh.service
I am not going to prevarication, this step also tripped me up a few times!
At present we should be gear up to effort our commencement connection via SSH. From the final on your Pi blazon:
ssh -five pi@<pi_IP>
Some of you may be asking: 'Now wait only a darned infinitesimal, why would I want to SSH from within my Pi?!?' Well, if yous are like me there is a proficient risk that your host and client will not be located in the aforementioned room. I must exist a sucker for punishment. If this describes your situation, information technology is therefore much more convenient to test whether or non SSH is working by logging in from the host for starters.
If all goes well you lot should see the following skillful news in your terminal:
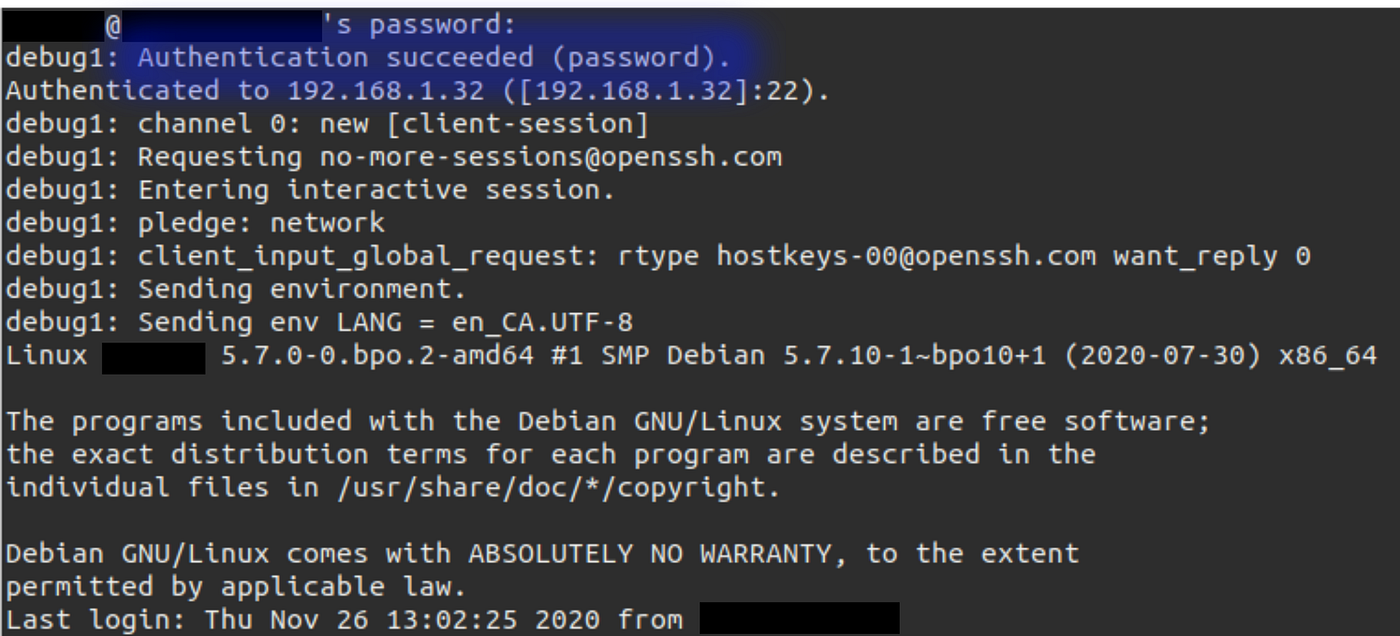
Provided you get the hallmark succeeded message y'all should exist able to log-in to your Pi via SSH from your customer machine. Go ahead, give it a try!
When logging in from your client y'all may notwithstanding get errors. Audit your SSH log file using the following command:
sudo nano /var/log/auth.log
Your our log may contain an error such as:
Invalid user <username> from server_IP port <port>
If this is the case, verify you are specifying the correct username in your config file for AllowUsers and attempt logging in once more.
Troubleshooting
If for some reason you lot are still unable to connect to your Pi via SSH there are a couple of additional troubleshooting steps you lot can perform, every bit per this forum mail:
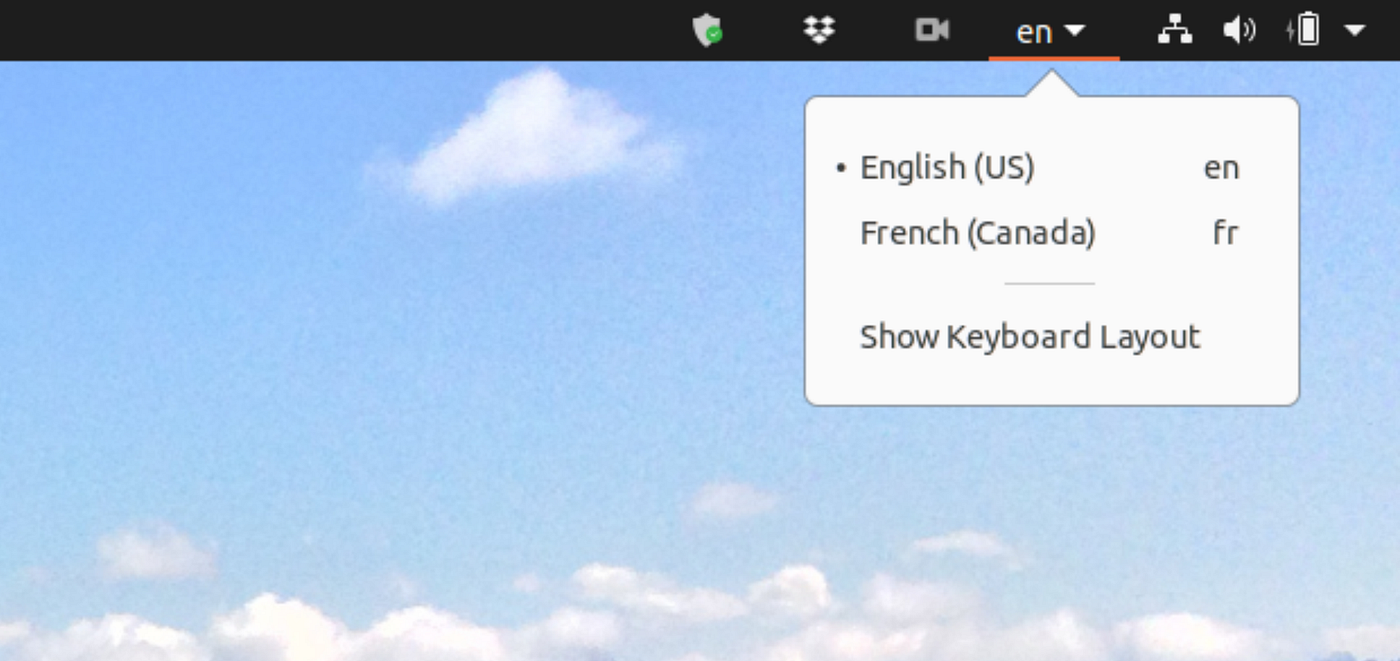
- Ensure your keyboard layout is correct between both the Raspberry Pi and your client machine (do not use a UK layout on your client when using an American-layout on the host, for example). On my Ubuntu machine I can cheque my keyboard layout at the summit correct-hand corner. At the take chances of sounding foolish, this has caused me more than than a tiny fleck of frustration the odd time when I become to log-in to something with a password only to discover my keyboard layout is speaking a unlike linguistic communication!
- From your client automobile, run:
dpkg-reconfigure openssh-server; encounter here for further details on this configuration pace. - Verify that yous have provided your Raspberry Pi with a static IP address in your router.
- Ensure you are logging into SSH with the correct username; you tin verify the username in one case yous are logged into your Pi. See the bespeak I fabricated just a few moments ago almost troubleshooting using
piequally the default user.
Hardening Your Pi with a PublicKey
Assuming all goes well and y'all are able to access your Pi via SSH you can set upwardly a public-individual key in order to improve the security. There is a good post that explains how to do it here and a more generic set of instructions tin can be found at this link. In this section I am going to expand the concept merely a wee chip past including a smashing style to manage your keys should you ever experience the need to have multiple server-customer SSH configurations. Every bit nerdy as information technology sounds, this is the kind of stuff that keeps me upwardly at night from time-to-time. Hopefully yous will find information technology helpful!
Important: These side by side steps will remove and re-install SSH keys on both your customer and server. Please please please: check with your System Administrator kickoff, especially if your server and/or client's SSH keys are configured for several other machines!
Delete Older SSH Keys
We will beginning by deleting whatsoever stale keys from the Pi, come across this video tutorial for details.
Navigate to the subconscious folder on your Pi containing the SSH keys:
cd .ssh
Next, edit the authorized_keys file:
sudo nano authorized_keys
Remove the entries from this file, they volition likely be rather long so exist patient when removing them.
Hit cntl-o then cntl-x to exit. Delete the authorized_keys file rather than messing with private keys, provided that your System Admin says it is okay to do and so. Bring them a prissy java or tea if this is your second or third visit!
Next, go to your client and remove the keys, see this post to remove the subconscious SSH folder on the client:
rm -rf /habitation/<client_user>/.ssh
Your SSH keys should now both be cleared from the server and client.
Generate New SSH Key on the Client
In this step we are going to generate a custom-named file to shop a key on our client, encounter this post for details. During this set-up we are going to split id_rsa keys into multiple files for better configuration control when dealing with multiple servers; this is handy particularly if you apply SSH PublicKey authentication at-dwelling house equally well as public services such as Git. In a Last on your customer, blazon:
ssh-keygen
Y'all may get the post-obit message:
Generating public/private rsa central pair.
Enter file in which to save the central (/home/<client_user>/.ssh/id_rsa):
/home/<client_user>/.ssh/id_rsa already exists.
Overwrite (y/n)?
You volition get this bulletin if you have already configured a public-private central for a dissever server. To avoid this message I recommend setting upwards separate keys per this mail.
At the prompt type:
/home/<client_user>/.ssh/id_rsa_<server_user>
If yous do not specify the total path the new key will be put where the system chooses, likely in the user's home folder. Be sure to specify the consummate path.
During the cosmos of your keys you may be prompted to set upwards a passphrase. I recommend using a passphrase if y'all are going to be using SSH to manage some other machine remotely via the Terminal. The passphrase is an added layer of security. If you plan on using SSH as part of some other service such as rsync you may want to not gear up a passphrase if your other scripts run in the background. I will leave this up to you lot and your Information Security folks to hash out. Bu-dum — bum.
Copy the new key to the server:
ssh-copy-id -i ~/.ssh/id_rsa_<server_user> <server_user>@<server_IP>
Configure the new SSH Key on the Client
Next we are going to create a config file to enable SSH to point to the appropriate keys, see this post for details:
touch ~/.ssh/config
cd abode/<client_user>/.ssh/
nano config
Once in the text editor, add the following:
Hit cntl-o to salvage, cntl-10 to exit.
Annotation: If you plan on connecting to additional hosts, put their lines beneath the first configuration in the file as follows:
Login to Raspberry Pi using SSH Public Key
With (one) your new SSH key generated, (2) issued to the Pi and (3) prepare-up in a configuration file on the client, y'all should now exist ready to log-in to your Pi using the PublicKey to confirm it is working. Y'all will want to ensure the PasswordAuthentication line is changed from yes to no, otherwise you may still be able to login to your server using a password. Once logged in via SSH to your Pi, edit its config file for the SSH daemon using sudo nano /etc/ssh/sshd_config to change the option for password-based logins:
# Modified YYYY-MM-DD by <author>.
#PasswordAuthentication yes
PasswordAuthentication no
As usual, hit cntl-o to save, cntl-ten to exit. Call up to restart ssh service subsequently editing the daemon config:
sudo systemctl restart ssh.service
You tin confirm that the change has taken result past logging out of SSH then attempting to log back in on the client machine. 1 of two things should happen: yous are logged in thanks to your public key, or, the organisation asks yous to enter your passphrase (assuming yous created one when you created your public-private cardinal-pair). If you lot go prompted to provide your passphrase you can striking enter a couple of times to meet if SSH then asks for a password. If information technology does not and so you accept confirmed that the public key is the approved method of hallmark.
PublicKey Troubleshooting
Life is not perfect and neither is setting up SSH the outset time. When things go sideways during your initial set-upward, there are a few things you tin can try. See my above caveat almost speaking with your System Administrator before proceeding further with the deletion of any keys from your client or server. If your System Admin happens to likewise be you then the chat should exist pretty quick! In no detail order:
- Delete
authorized_keyson the server, they are located in the/.sshbinder. - If you are using Ubuntu, delete your
OpenSSHkeys from the UbuntuPasswords and Keysapp on your client. I beleive this program goes by the name ofSeahorsewhen invoked from the control line. - Delete the
/.sshfolder on your customer for both your user as well every bit root accounts, elevate to root usingsudo su, thenrm -rf /root/.sshBe very careful with this command as information technology volition delete other things on your system willy-nilly if non used correctly! - Turn your client off and back on once more to purge any buried keys stored in environment variables. Yes. I only told you to turn it off and back on once more.
- Change the
hostnameon your client temporarily to help troubleshoot stale keys. Inspectingauthorized_keyswith a text editor to ensure all keys with the formerhostnamewere removed. - Utilise the following command to ensure stale keys are no longer present:
ssh-add -fifty - If you see any keys every bit well equally your old
hostnamelater running the above command, it is a good indication that there are stale keys somewhere on your organization, get back and repeat the above steps to purge them. - Re-generate keys for the server and client, use nada passphrase by hitting enter when prompted.
- Use
ssh-add -fiftyto ostend the newly-generated keys as well equally ensure that both theusernameandhostnameare correct. - If all else fails go and grab a nice beverage then endeavor again tomorrow.
Special Bonus: Interactive SSH
SSH should ship with ten-tools to permit you to open graphical windows with the Ten selection.
Open a new SSH session as follows:
ssh -X pi@<pi_IP>
You should now be able to blazon in the names of programs on your server and striking enter. If all goes well the program should open as a new window on your client. Be patient particularly if you are connecting via WiFi!
Summary
Here are the abbreviated steps for this article, for those that want to cutting right to the hunt.
Server
Verify SSH is enabled on your Raspberry Pi by navigating to the 'raspberry' icon in the bill of fare and select Preferences, Raspberry Pi Configuration. In the Interfaces tab, select Enable for SSH. Close the menu.
Install openssh-server via:
sudo apt install openssh-server
Ostend SSH is running:
sudo service ssh status
Edit the SSH daemon configuration:
sudo nano /etc/ssh/sshd_config
Un-comment PubkeyAuthentication:
# Modified YYYY-MM-DD by <author>.
PubkeyAuthentication yeah
Uncomment PasswordAuthentication:
# Modified YYYY-MM-DD by <author>.
PasswordAuthentication yes
Add an AllowUsers line directly below PasswordAuthentication as follows:
# Modified YYYY-MM-DD by <writer>.
AllowUsers pi
Comment-out AllowGroups if it is nowadays:
# Changed on YYYY-MM-DD by <writer>.
# AllowGroups …
Salve by hitting cntl-o then cntl-10 to exit then restart your SSH daemon:
sudo systemctl restart ssh.service
Attempt an initial SSH connection from the last on your Pi:
ssh -v pi@<pi_IP>
You should at present be logged into an SSH session on your Pi. Log-out and and then proceed with setting upwards PublicKey access.
Become and check with your Organization Administrator to confirm if they are okay with y'all deleting the SSH keys earlier proceeding with these next steps!
Navigate to the hidden folder on your Pi containing the SSH keys:
cd .ssh
Edit the authorized_keys file:
sudo nano authorized_keys
Remove the entries from the file then hitting cntl-o to salvage and cntl-x to exit. Alternatively, delete the entire file via:
rm /habitation/<client_user>/.ssh/authorized_keys
Client
Remove old keys on the client:
rm -rf /home/<client_user>/.ssh
Generate a new ready of SSH keys:
ssh-keygen
During key generation, specify the path and rename the new cardinal file along the lines of:
/home/<client_user>/.ssh/id_rsa_<server_user>
Specify a passphrase as applicable.
Copy the new key to the server:
ssh-copy-id -i ~/.ssh/id_rsa_<server_user> <server_user>@<server_IP>
Ceate and edit a config file to enable SSH to point to the newly-created cardinal:
bear upon ~/.ssh/config
cd home/<client_user>/.ssh/
nano config
One time in the text editor, add together the following:
Hit cntl-o to save, cntl-x to exit.
Connect to Server
With (one) your new SSH key generated, (2) issued to the Pi and (3) fix-up in a configuration file on the client, you should at present be set up to log-in to your Pi using the PublicKey to confirm information technology is working.
Login to your Pi from the client:
ssh -v pi@<pi_IP>
You should be asked for your passphrase assuming you set one up.
Edit the config file:
sudo nano /etc/ssh/sshd_config
Change the PasswordAuthentication line is changed from yes to no, otherwise you may withal be able to login to your server using a password:
# Modified YYYY-MM-DD by <author>.
#PasswordAuthentication yes
PasswordAuthentication no
Hitting cntl-o to salvage, cntl-ten to exit then restart your SSH daemon:
sudo systemctl restart ssh.service
Logout and login once more from the customer to confirm PublicKey still works.
Postscript
I strongly recommend you take boosted steps to harden your RaspberryPi following this tutorial, particularly when it comes to SSH. There are several posts that go into further particular in this regard such as this one. And too this. This one too.
At that place are many more things you tin can do to improve the connectivity between your Raspberry Pi and some other calculator, for instance please bank check out this excellent Medium article on connecting an RPi to a Mac with an Ethernet cablevision. You may need to conform your DNS settings in one case you perform this connection, more than on this in another postal service!
Another useful tip is to map your server's hostname to its IP accost. This step is useful when you wish to connect with your new automobile via SSH. Think of it like a shortcut for your server'due south IP! More than info on this in some other mail.
What steps have you lot taken to ready SSH on your Raspberry Pi?
crenshawbaccustelic.blogspot.com
Source: https://medium.com/swlh/get-ssh-working-on-a-raspberry-pi-4-50f7c8bafe16
0 Response to "Permission Denied Please Try Again Raspberry Pi Pi Bakery"
Mag-post ng isang Komento